Active Directory Federation Services using OIDC
Follow the steps below to configure single sign-on (SSO) for Claris Studio with your Active Directory (AD) instance’s Federation Services using OpenID Connect (OIDC). To establish trust between your AD instance and your Claris Studio team, you’ll need to:
-
Create an application group.
-
Add transform rules.
-
Enter data in Claris Studio.
Open the Claris Studio setup page
-
Sign in to your Claris Studio team.
-
Click the Users tab on the left, then click Configure External IdP.
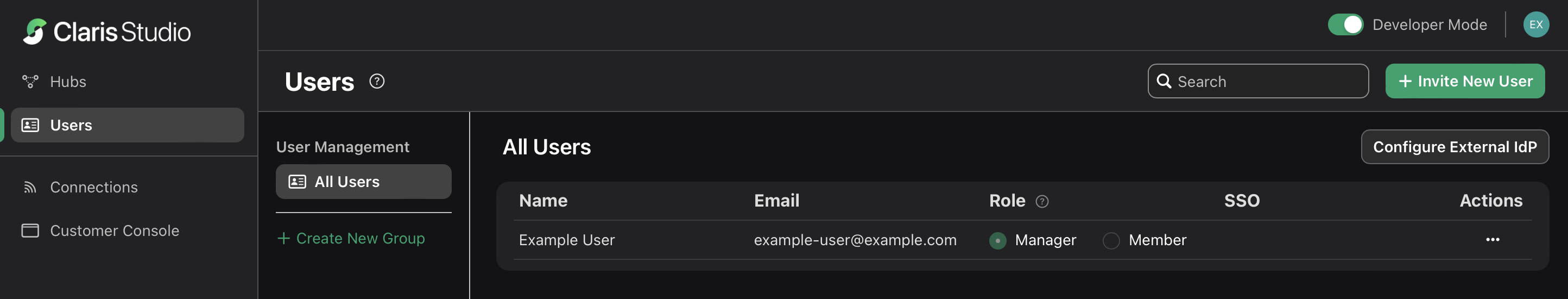
-
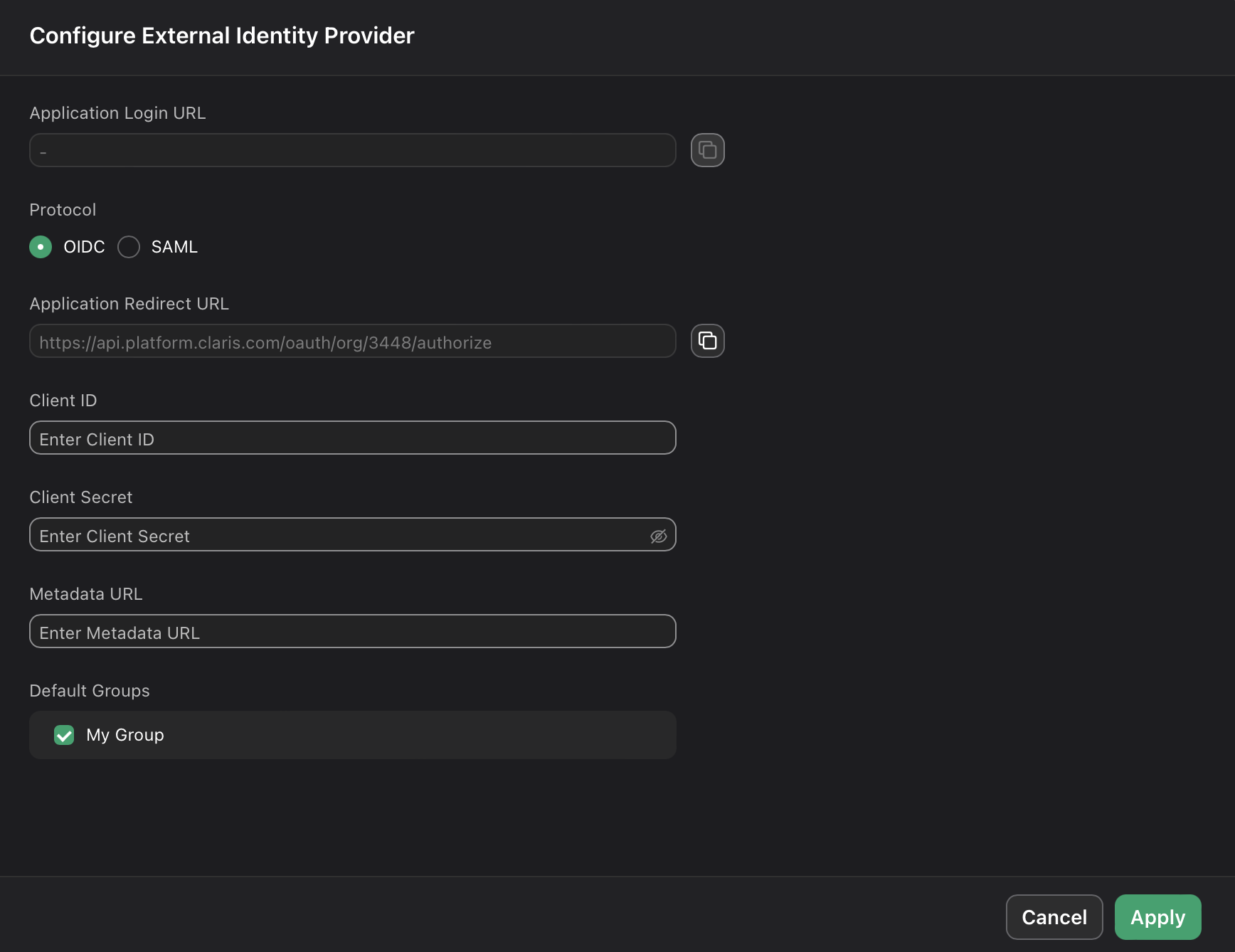
In the Configure External Identity Provider dialog, for Protocol, choose OIDC. Keep this page open to come back to later.
Add an application group
-
In your Windows Server instance, sign in with your administrator account. From the Start menu, click
Windows Administrative Toolsunder theWindows Serversection on the right.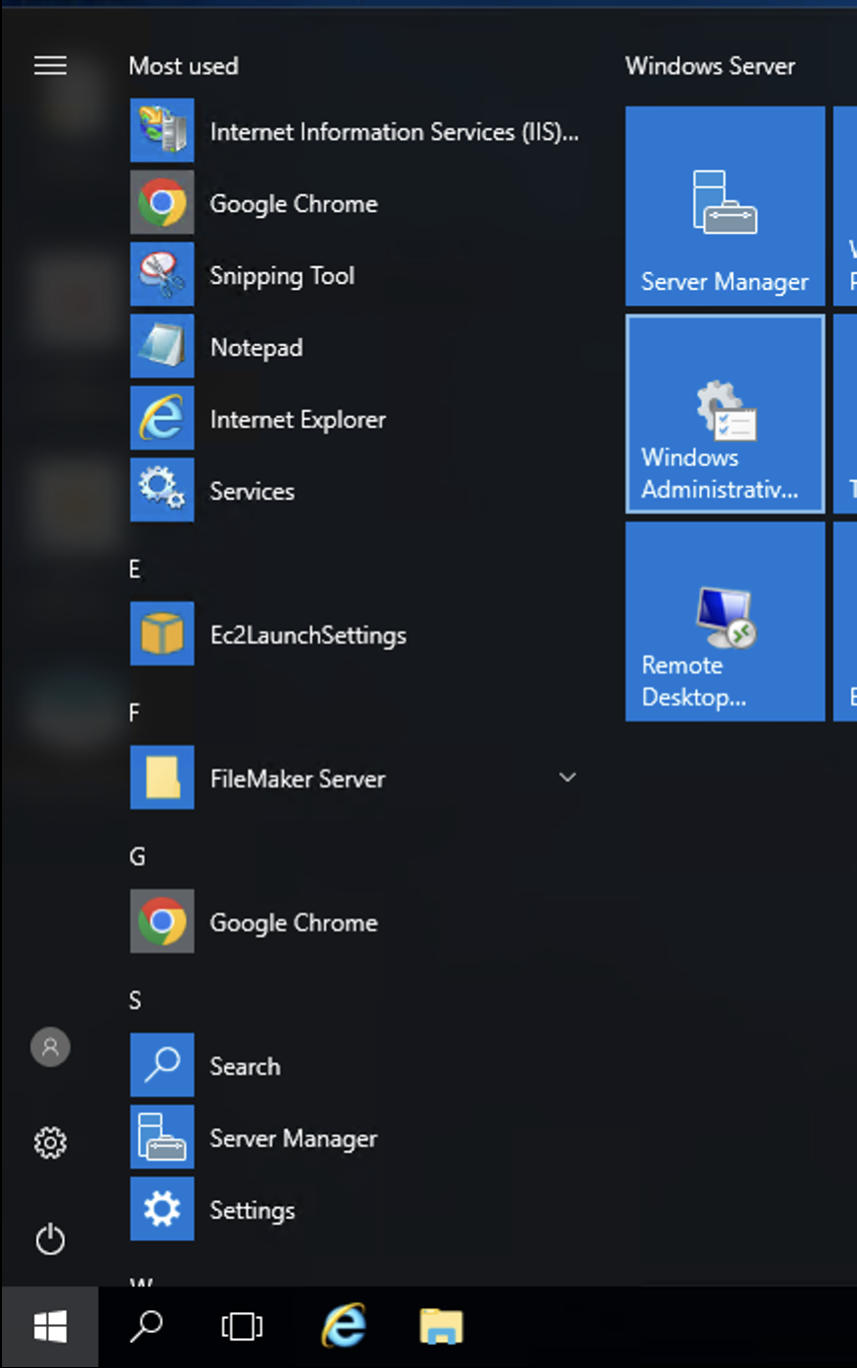
-
In the new File Explorer window, open the
AD FS Managementshortcut.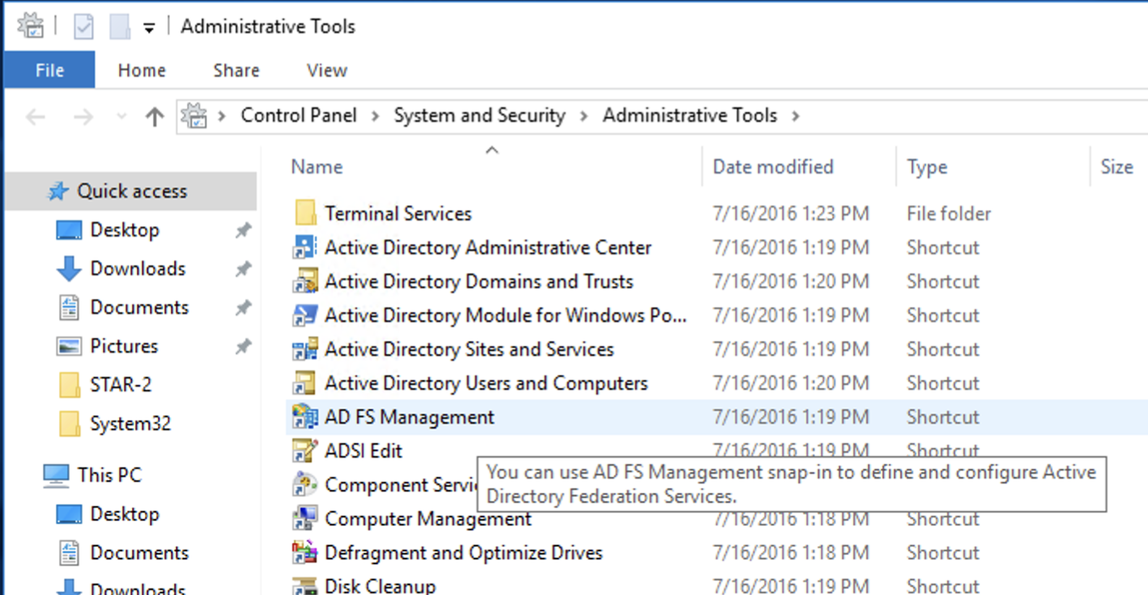
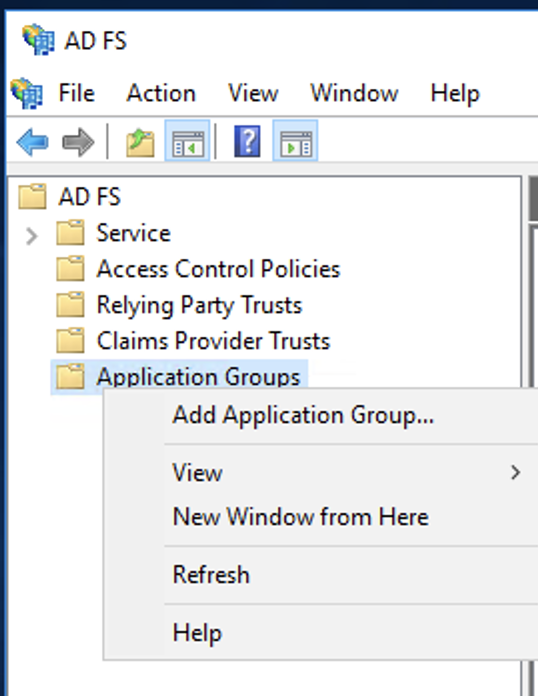
-
In the left sidebar of the AD FS window, right-click Application Groups > Add Application Group.
-
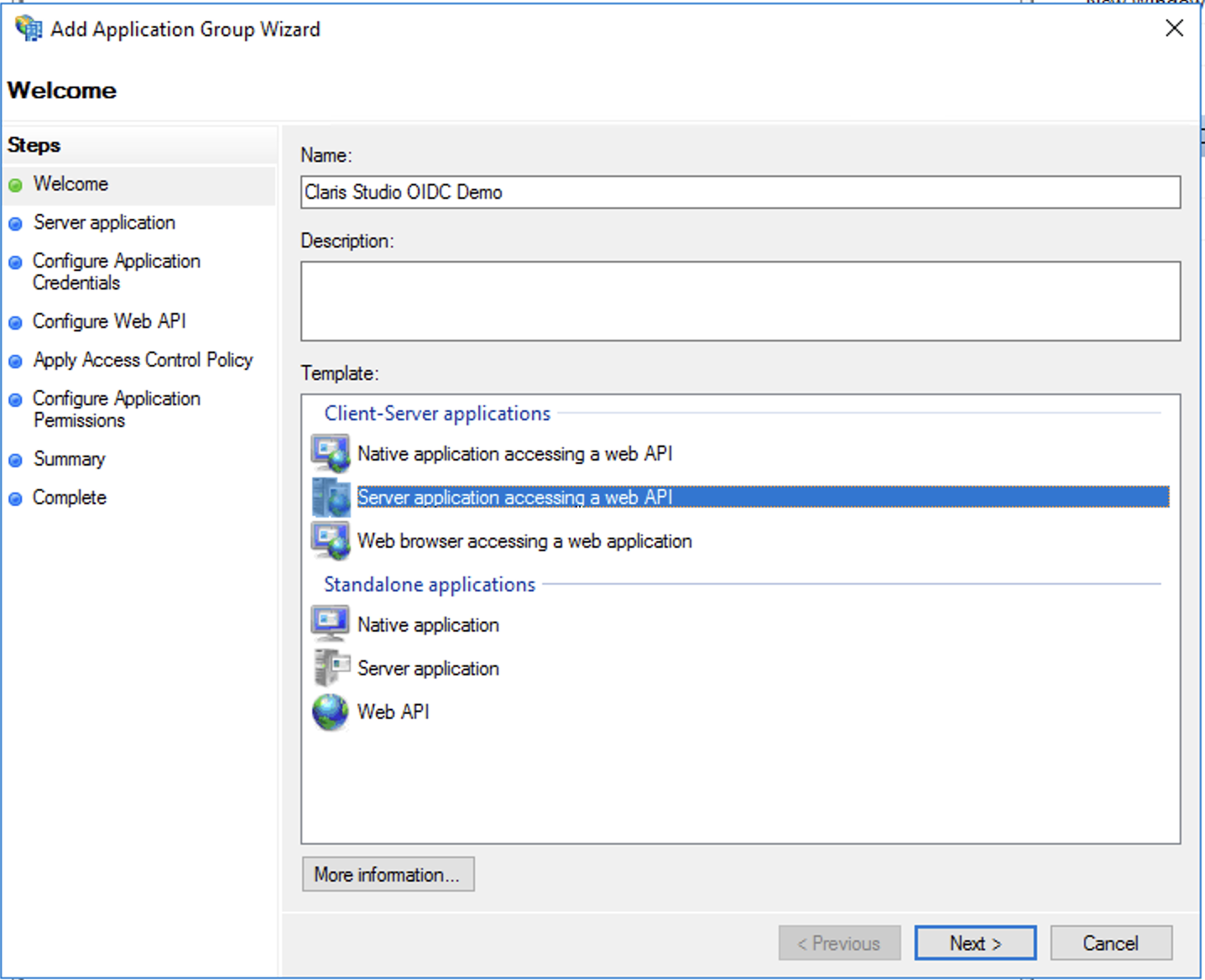
In the wizard, give your new integration a name to distinguish it from any other integrations you might have, then select the Server application accessing a web API option. Click Next.
-
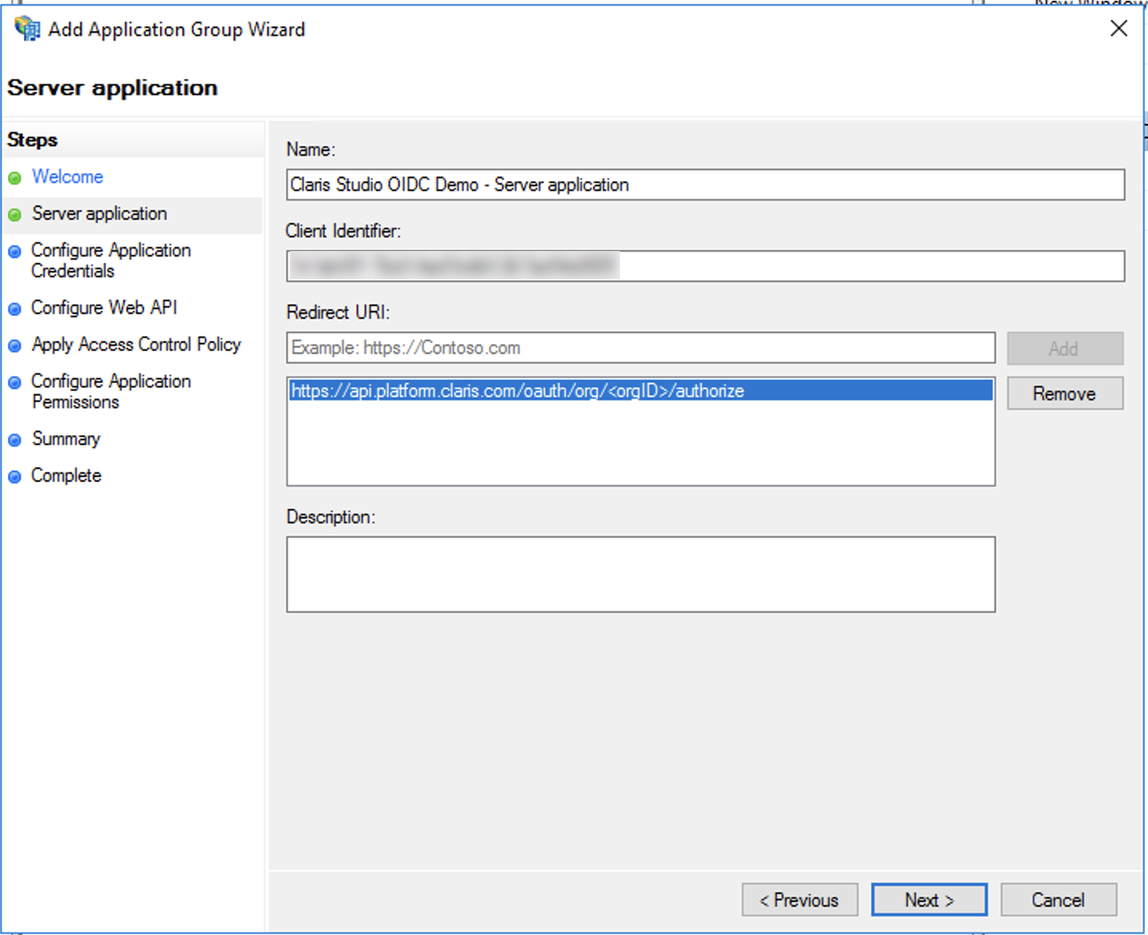
In Claris Studio, copy Application Redirect URL (see “Open the Claris Studio setup page” earlier) and paste it in the Redirect URI field. then click Add.
Additionally, copy Client Identifier value and save it somewhere secure where you can retrieve it later. When you’re finished, click Next.
-
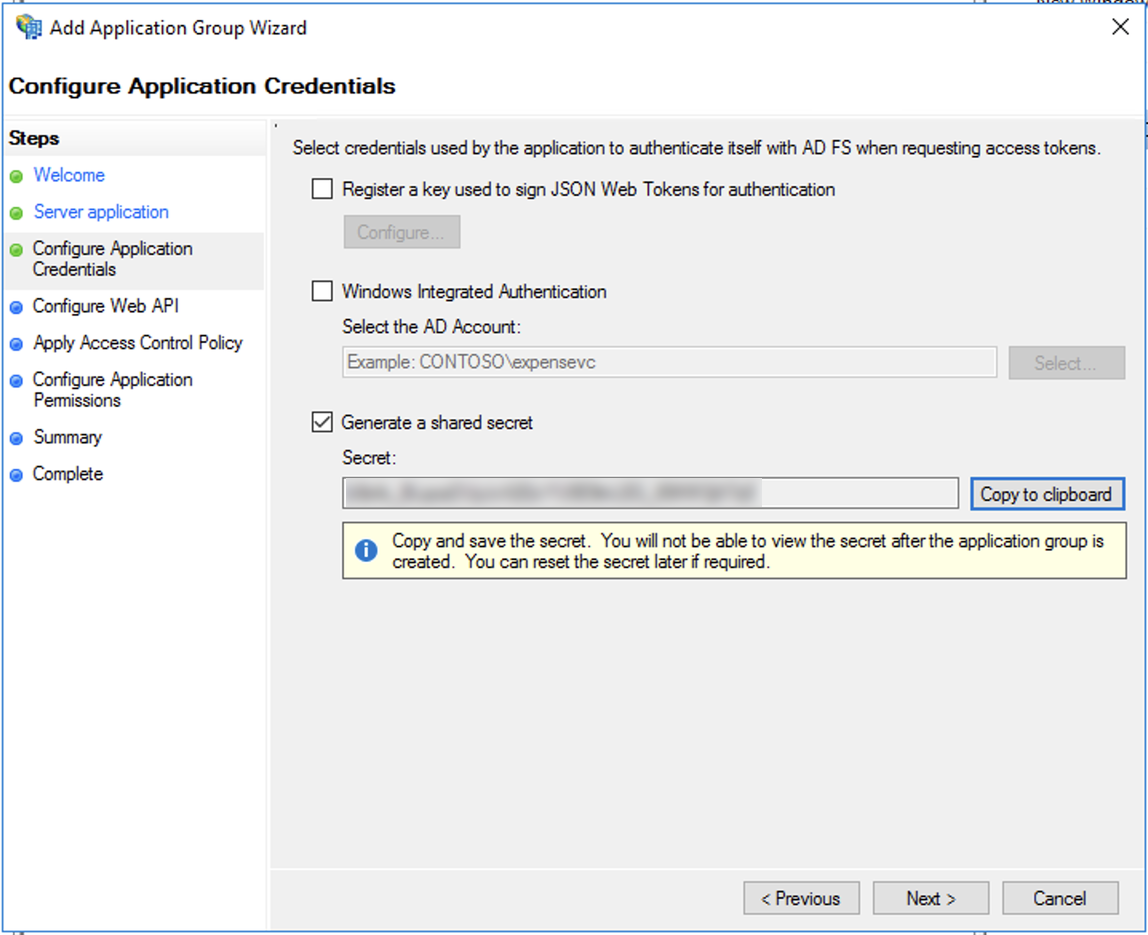
Select the Generate a shared secret option, then click Copy to clipboard. Paste the value somewhere secure where you can retrieve it later.
Be sure to label it as separate from the Client Identifier you saved in the previous step. When you’re finished, click Next.
-
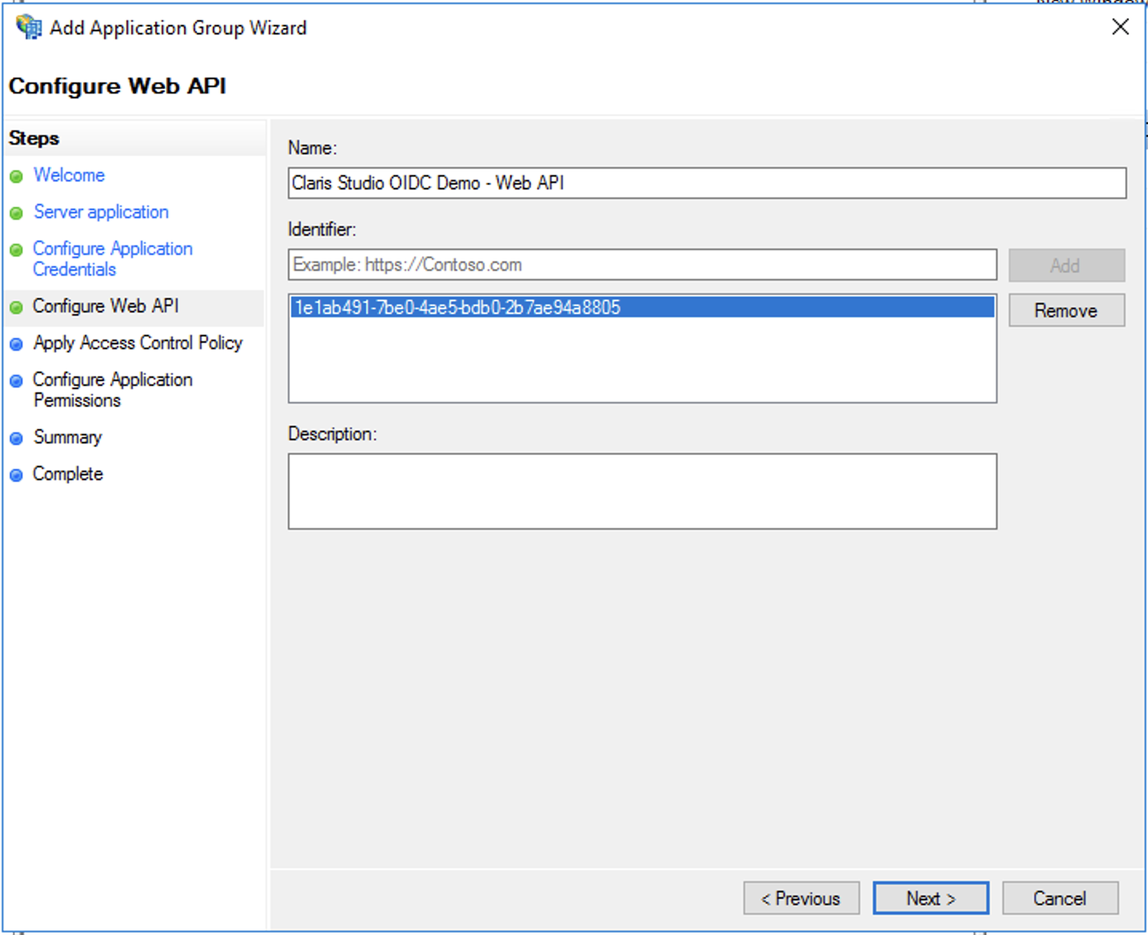
Copy the Client Identifier you saved earlier and paste it into the Identifier field, then click Add. Click Next.
-
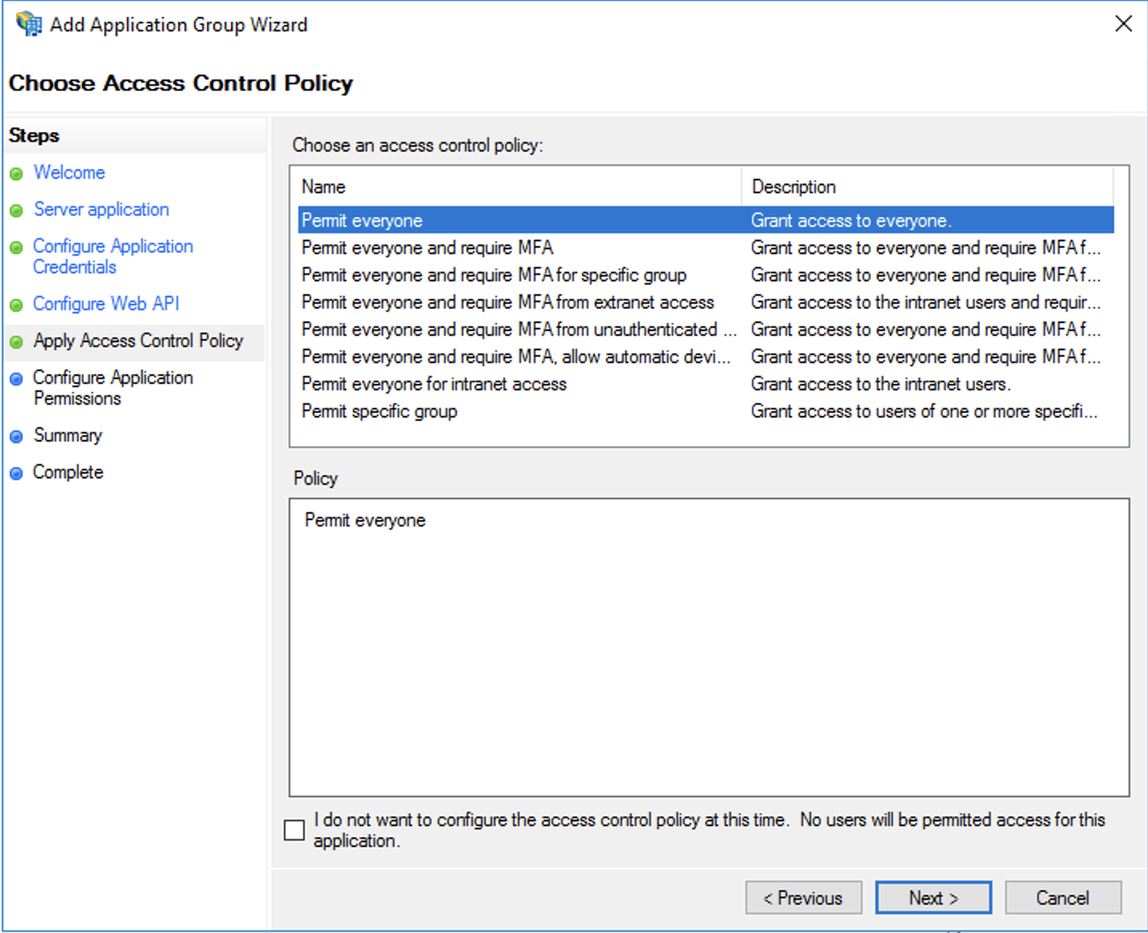
Choose an access level for your Active Directory users who should be able to access the integration. Leave Permit everyone selected if anyone should be able to access your Claris Studio team. Click Next.
-
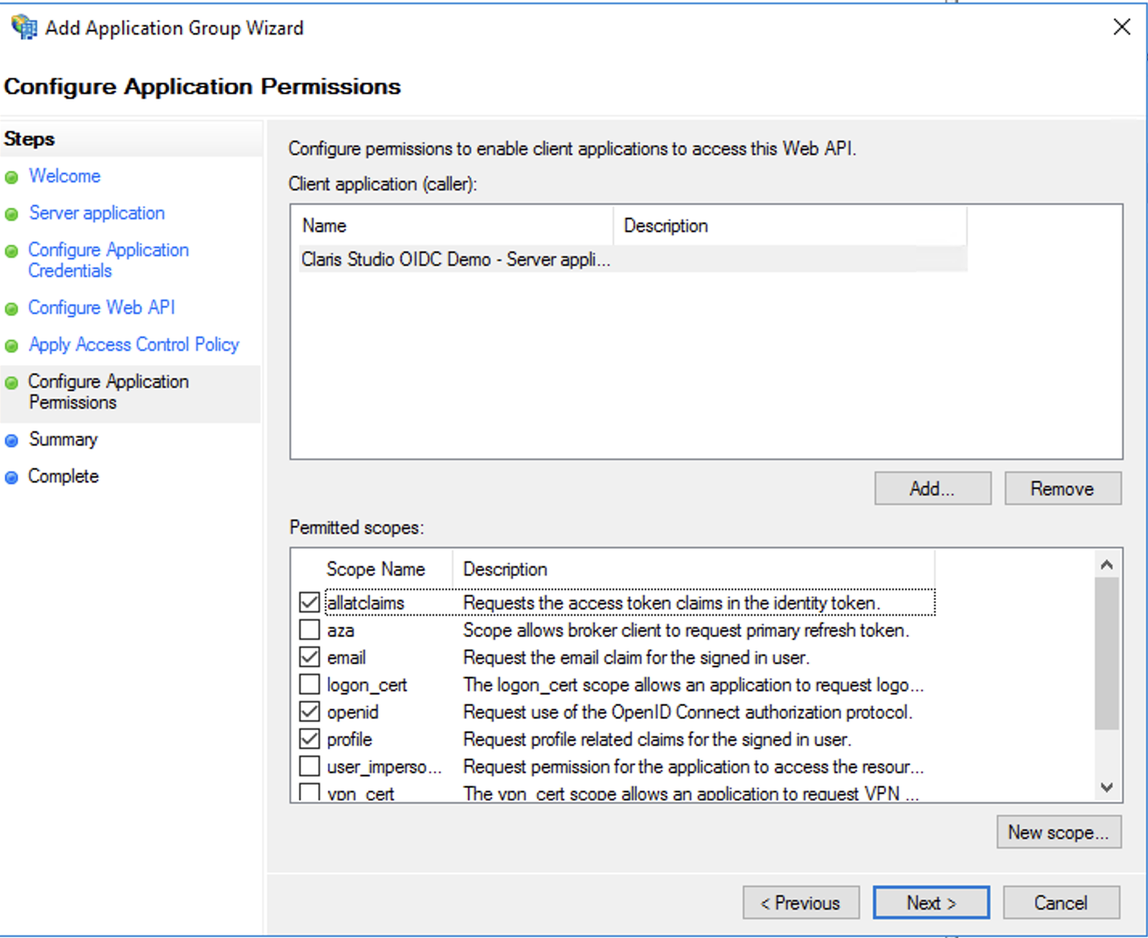
For Permitted scopes, be sure that the following items are selected. Some may already be selected.
-
allatclaims
-
email
-
openid
-
profile
Click Next.
-
-
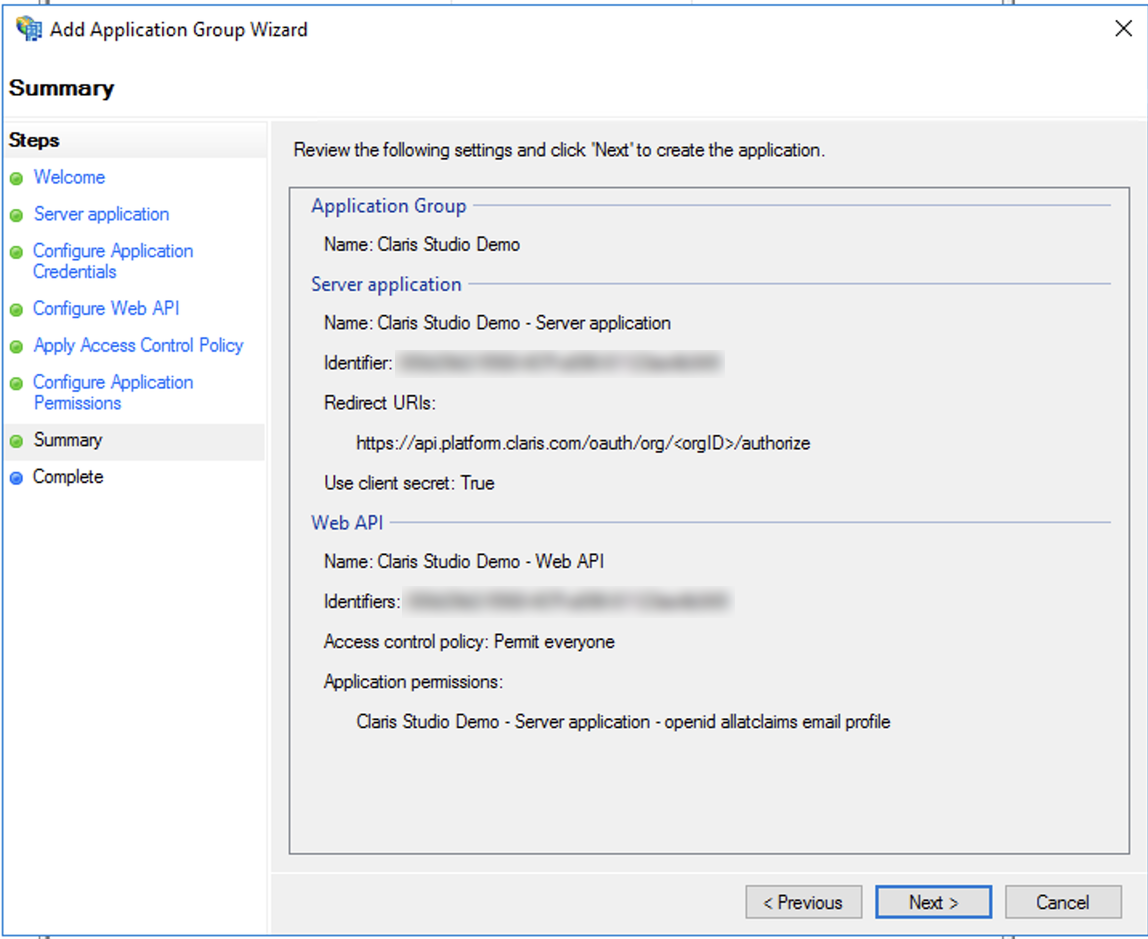
On the Summary screen, click Next.
Add transform rules
-
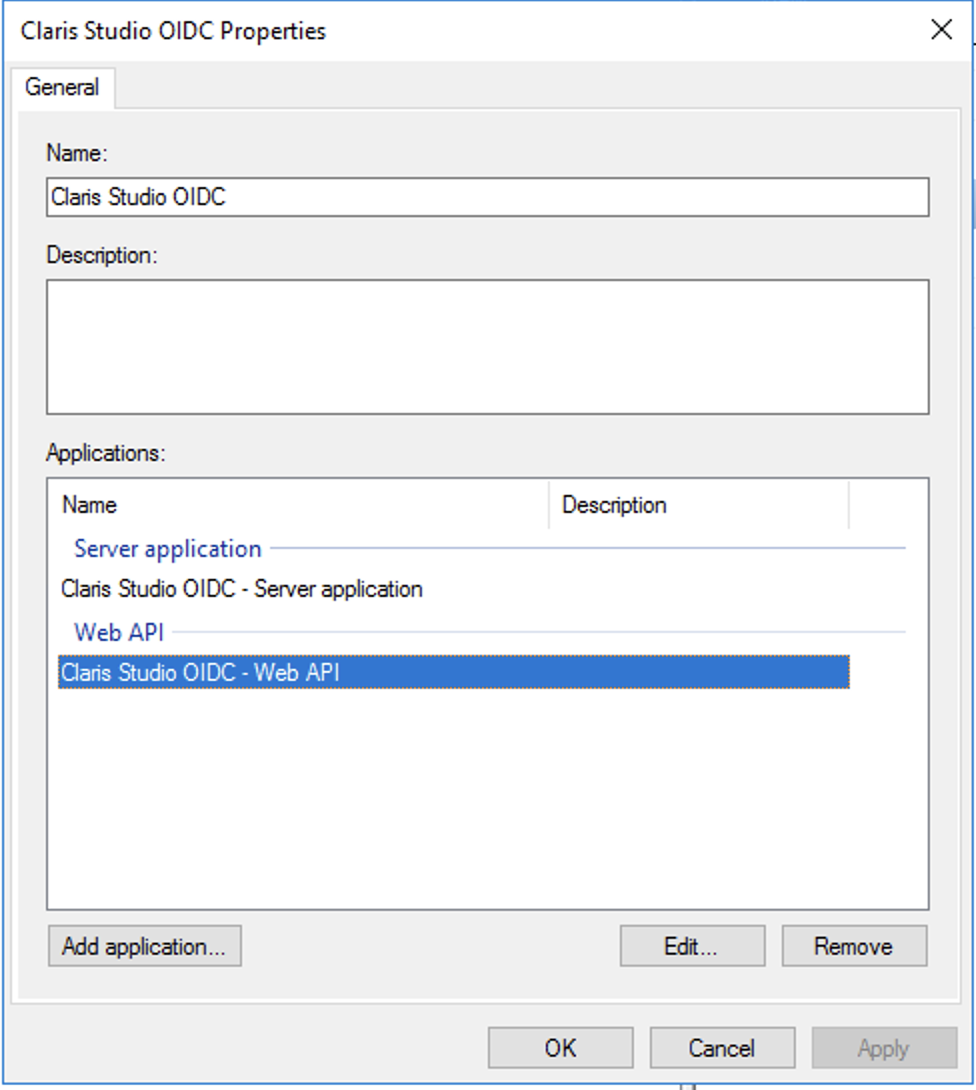
In the AD FS window, double-click the application group that you just added. Then under Web API, select the row for your integration and click Edit.
-
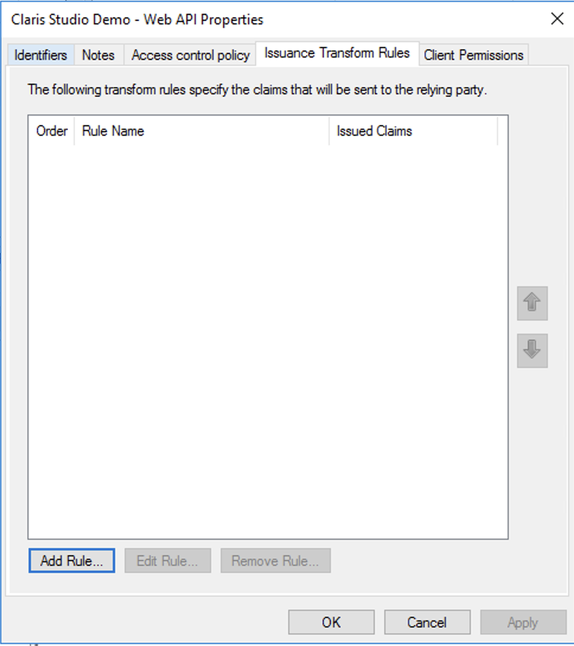
In the Web API Properties dialog for you application, click the Issuance Transform Rules tab. Then click Add Rule.
-
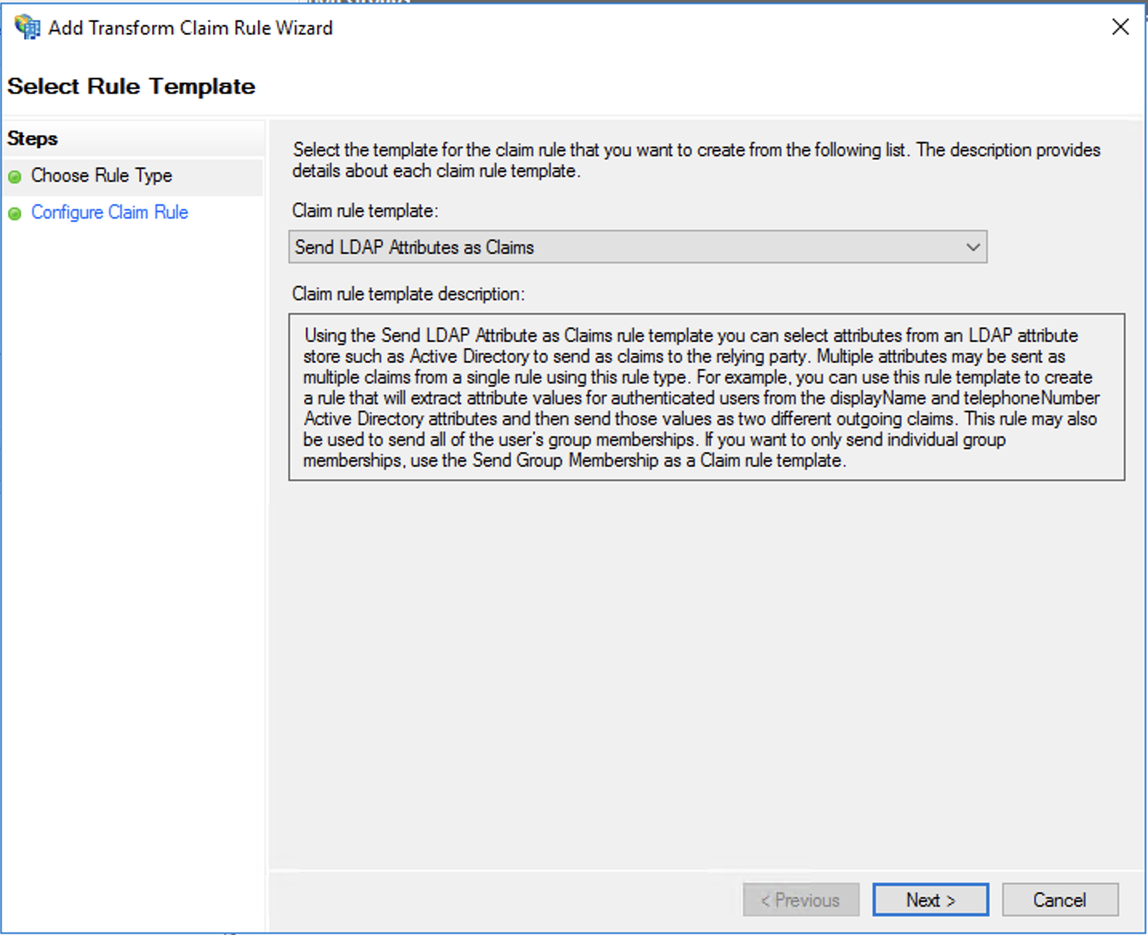
In the wizard to add claims, for Claim rule template, leave Send LDAP Attributes as Claims selected. Then click Next.
-
For Claim rule name, give the claim rule a descriptive name. For Attribute store, select Active Directory. Then, add the following LDAP attribute mappings for each row.
The LDAP Attribute can be selected from the drop-down menu or autocompleted, but values for Outgoing Claim Type must be entered exactly as shown, because they are case sensitive.
-
E-Mail-Addresses → email
-
Given-Name → Given Name
-
Surname → Family Name
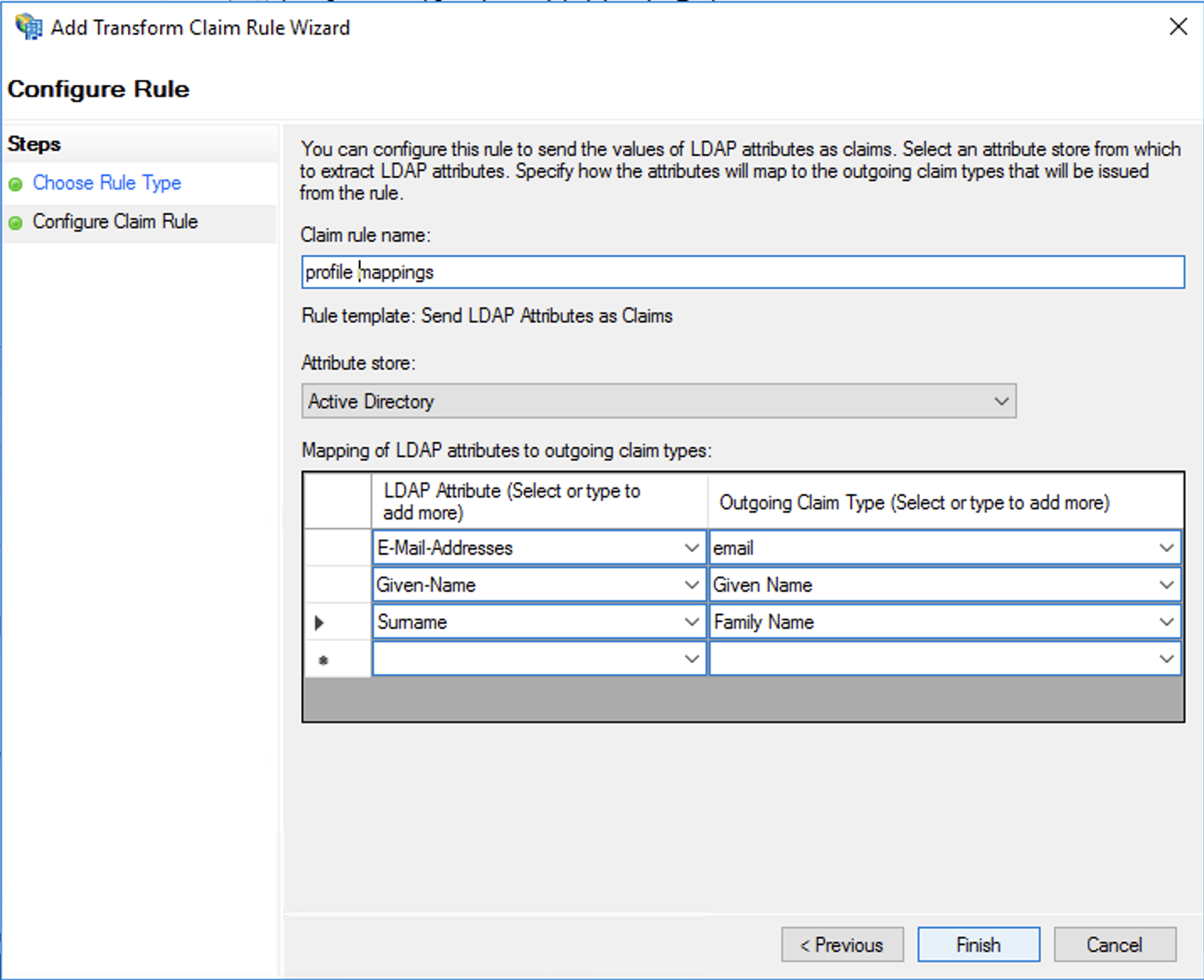
Click Finish when done.
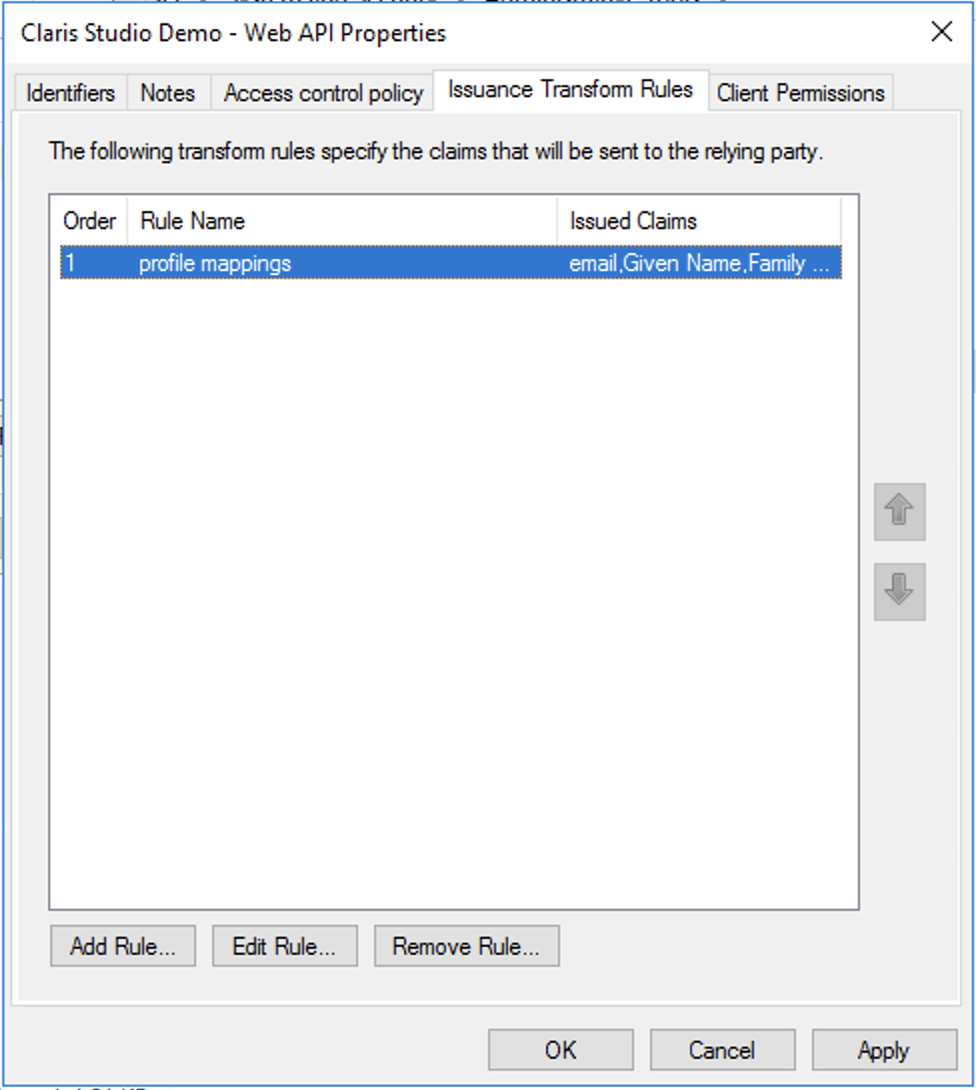
Finally, in the dialog, click Apply.
Enter values into Claris Studio
- Go back to the Claris Studio page you opened earlier (see “Open the Claris Studio setup page”).
-
In the Configure External Identity Provider dialog, for Protocol, choose OIDC, then provide the following information:
-
Client ID: the Client Identifier token you stored in step 4 of “Add an application group”
-
Client Secret: the Client Secret token you stored in step 5 of “Add an application group”
-
Metadata URL:
https://<AD FS Domain>/adfs/.well-known/openid-configurationwhere <AD FS Domain> is your AD FS domain name or IP address -
Select one or more Default Groups that you want to sign in using this external IdP, then click Apply.
If you have no groups, you can create one here and add users to it later. See Work with groups for more information.
- On the Users page, copy the link labeled Application Login URL and provide it to users. Using this URL enables them to sign in to Claris Studio with their SSO credentials.